Microsoft recently released a new feature of their Windows 10 operating system called “Windows Sandbox” as a preview to the Windows Insider program. Windows Sandbox allows users to launch a secure virtual instance of Windows 10 within their existing environment to visit websites, test new apps or work with files. Microsoft describes its newest feature as follows:
Windows Sandbox is a new lightweight desktop environment tailored for safely running applications in isolation.
A malware analysis environment needs to meet the following requirements:
- Non-persistence
The environment needs to be in pristine condition at every launch. Changes need to be discarded after analysis has been completed. - Isolation
Malware must not be able to escape the analysis environment. - Rich tool set
Applications required by the malware analyst need to be pre-installed in the environment. - Disabled malware detection
Active malware detection will hamper the analysis.
Non-persistence

The dynamic image contains links to the host operating system. Credit: Microsoft.com
Isolation
Malware analysis needs to be conducted in an isolated environment. Most hypervisors can be configured in a way that disables any communication between the guest and the host or the network. Windows Sandbox uses configuration files to configure the environment. Options like network access and access to local folders on the host can be configured. It is even possible to configure access to local folders as read-only as a way to transport files into the sandbox and prevent malware to write to the same folder. Unfortunately, it is currently not possible to disable access to the clipboard as this is the designated method of transportation of files between the sandbox and the host. It might allow a malware to use this channel to escape the sandbox.
<Configuration> <Networking>Disable</Networking> </Configuration>
Configuration files have a *.wsb file extension which is assigned to the Windows Sandbox feature. When double clicking a wsb file, Windows Sandbox is started with the respective configuration, which is very handy when working with different configuration files.
Tool set
<Configuration> <Networking>Disable</Networking> <MappedFolders> <MappedFolder> <HostFolder>C:\MalwareAnalysis</HostFolder> <ReadOnly>true</ReadOnly> </MappedFolder> </MappedFolders> </Configuration>
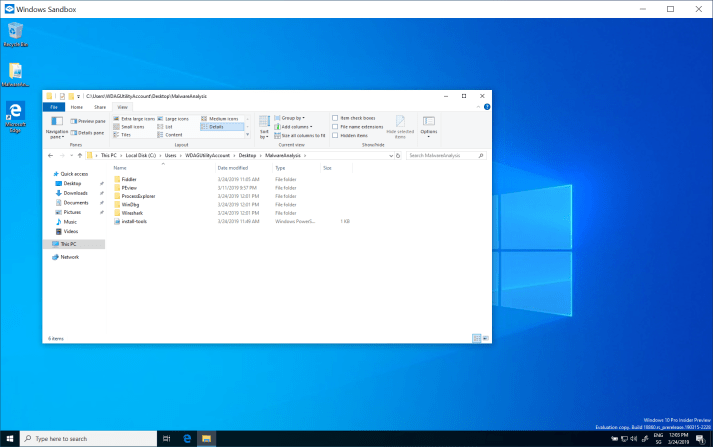
A local folder is mounted into the sandbox and placed on the desktop.
#Install Fiddler $program = "C:\Users\WDAGUtilityAccount\Desktop\MalwareAnalysis\Fiddler\FiddlerSetup.exe" $arguments = "/S" start-process -FilePath $program -ArgumentList $arguments
<Configuration> <Networking>Disable</Networking> <MappedFolders> <MappedFolder> <HostFolder>C:\MalwareAnalysis</HostFolder> <ReadOnly>true</ReadOnly> </MappedFolder> </MappedFolders> <LogonCommand> <Command>powershell.exe -executionpolicy bypass -file "C:\Users\WDAGUtilityAccount\Desktop\MalwareAnalysis\install-tools.ps1"</Command> </LogonCommand> </Configuration>

Fiddler was installed successfully.
Disabled malware protection

Windows Defender is turned off by default.
Closing thoughts
The answer to the titular question is definitively: it depends.
Windows Sandbox is indeed lightweight and free. When it comes out of preview, it will be part of the Professional and Enterprise editionsof Windows 10. While it is not as feature rich as professional sandboxes such as cuckoo or Joe Sandbox, with a little effort towards automation using its scripting support, it can definitively do the job.
One thing to keep in mind is the preconfigured access to the clipboard. I do hope that access to the clipboard can be configured in the same manner that access to local folders can when it comes out of preview. This would give malware analysists complete freedom when deciding how to transport malware into the sandbox.

One thought on “Can Microsoft’s Windows Sandbox feature be used to analyse malware?”